Microsoft 365 Security Assessment
🛠 Challenge 🛠
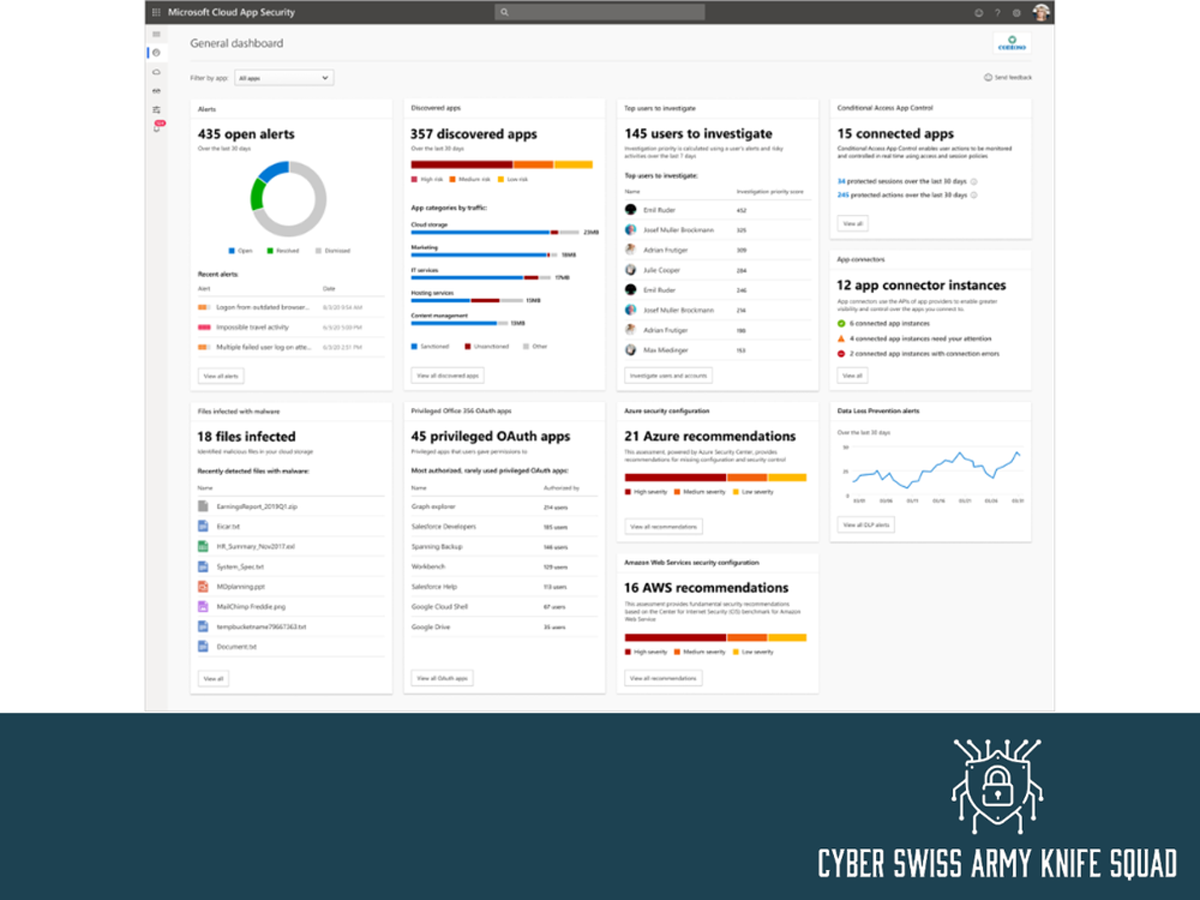
🎯 The environment is not safe for cloud-based users.
🎯 The environment is not in accordance with standard security benchmarks such as CIS.
🎯 There is a lot of phishing and other compromise going on in the email environment.
🎯 According to Microsoft’s standard approach, the security score appears to be quite low.
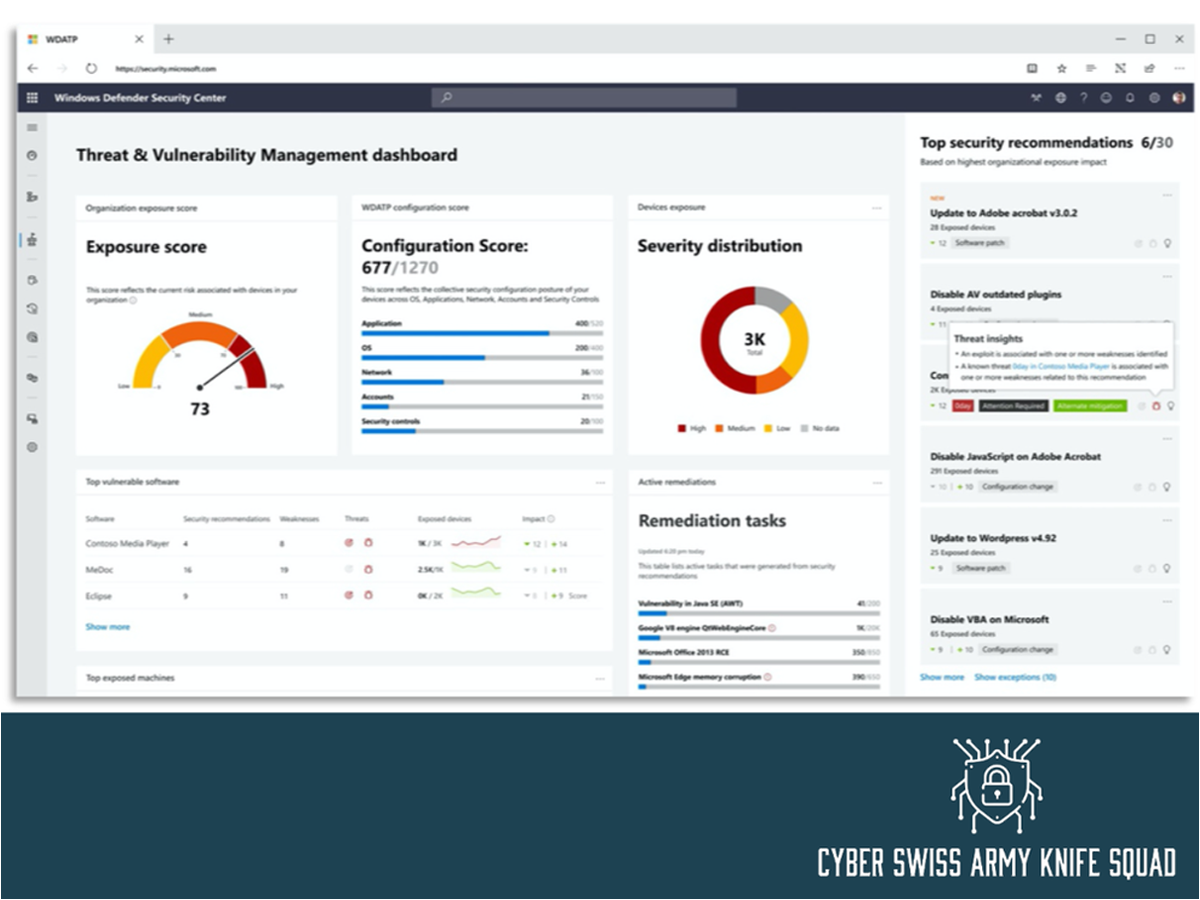
🎯 Endpoint devices are not secured against ransomware and other related threats.
🎯 There is no single report provided to check protection against the entire environment, including Azure, Office 365, Data, and Endpoint.
🛠 Solution 🛠
✅ Several workshops were held to explain the concept and identify current pain points.
✅ Explain the requirements and walk the client through the existing license posture.
✅ Describe similar situations in the lab and what to expect.
✅ Provide a comprehensive report on the current user posture.
✅ Develop thorough project plans outlining how we will onboard each user segment based on their needs.
✅Based on the conversation and agreed-upon strategy, I designed the solution.
🛠 Outcome 🛠
🤝Every day, detailed reports are given out to indicate the success of the current activity.
🤝We were able to deliver the assessment well ahead of schedule thanks to well-planned project execution.
🤝Client understood the security posture and engaged me to improve it.