Microsoft Azure Sentinel Configuration, Workshop, & Enhancements
🛠 Challange 🛠
🎯 Implement Microsoft Security tools such as Defender for Identity, Defender for Endpoint, Defender for Cloud Azure Defender, O365, MCAS, Conditional Access and DLP.
🎯Configure Azure Sentinel from the ground up, connecting on-premises and MS Native Data connectors.
🎯Explain all of Azure Sentinel’s capabilities. Deliver the whole sentinel project.
🛠 Solution 🛠
✅ Conducted a number of workshops to explain the concept and identify present pain areas.
✅ Walk the customer through the current license posture and explain the requirements.
✅ Walkthrough similar events in the lab and explain what to expect.
✅ Implement various Security defender products – Identity,O365,MCAS,Endpoints and DLP
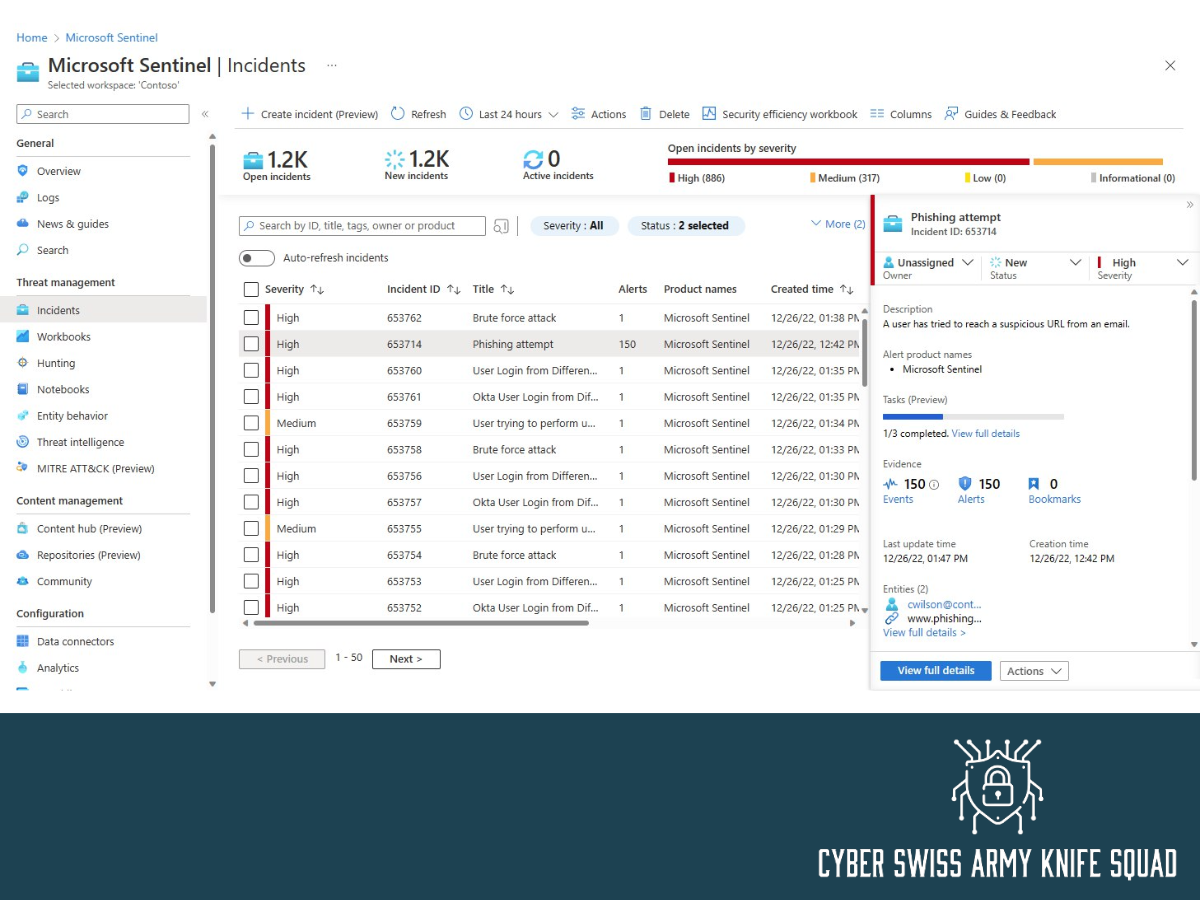
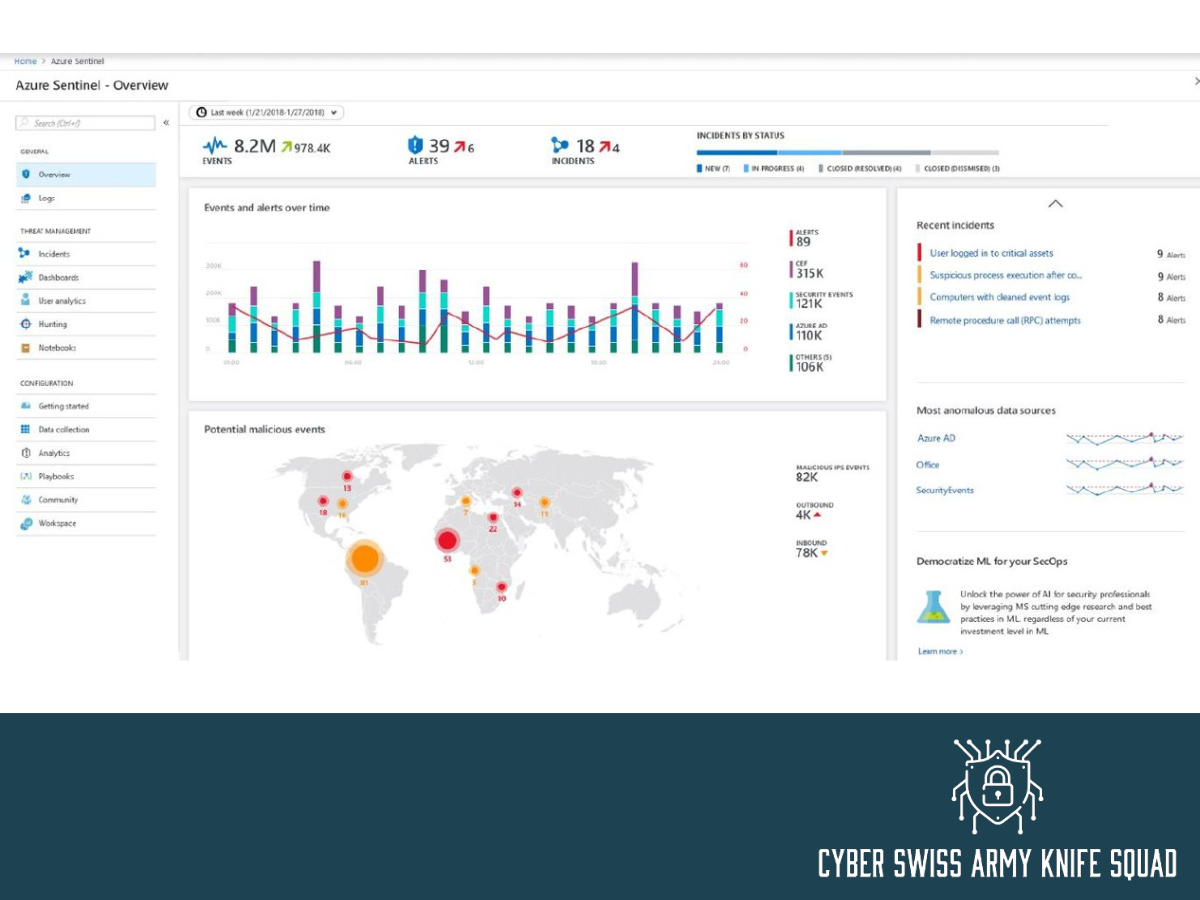
✅ Carry out project delivery tasks Connect several native data connectors, analytics rules, and other E5 security products such as Defender for Identity, O365, MCAS, Azure Activity and Sign-in logs to Sentinel.
✅ Run the setup with the current Technical leaders and explain the various workbooks, issue management, investigative approach, and playbook automation.
✅ Handover the solution to the Internal team
🛠 Outcome 🛠
🤝 Completed the deployment of all Defender products
🤝 Sentinel’s native data connectors have all been deployed.
🤝 As the end-user is ready to manage Sentinel problems, they can use hunting functionality to monitor their environment both reactively and proactively.